Zoom meeting security is largely a matter of which settings and options you choose. This post contains some of OIT’s recommendations for securing your Zoom meetings.
Step 1. Update Zoom
Before you do anything else, be sure your Zoom software is up to date! Certain options and features may not be visible or available to you if you are using an older version of the Zoom software.
Step 2. Learn how to access your settings
The settings you choose can greatly increase security. But the more secure you make Zoom, the more steps may be required for your participants to enter meetings, and the more involved you as the host must be in managing the meeting.
The settings described in this article are not all required to be set as shown. You must decide how best to manage your Zoom experience with your given audiences. Some settings can be controlled or toggled on and off while a meeting is in progress from controls within the Zoom meeting itself, making it easier to adjust as needed.
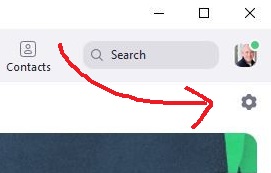
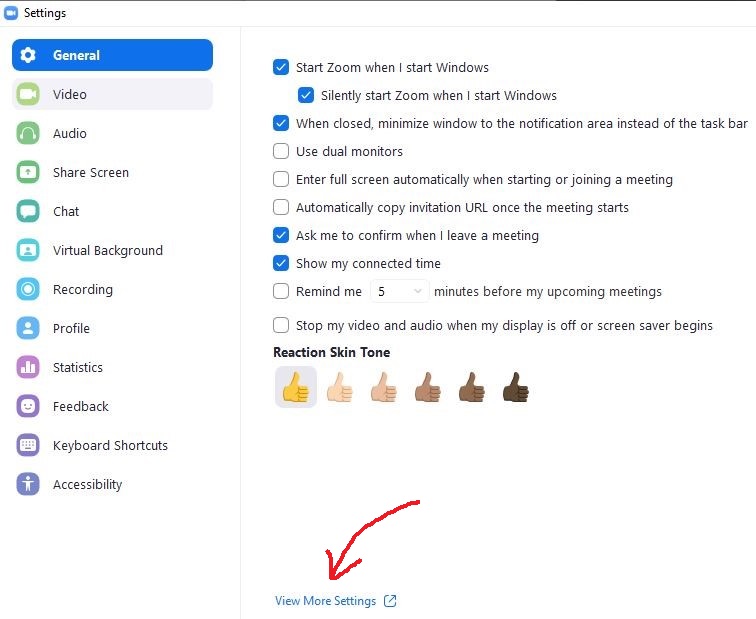
To change the settings and permissions within your Zoom account open your Zoom desktop Client and click the gear icon for settings. Then click View More Settings to open a web interface with all your account settings.
In general, the larger and more public your Zoom audience is, the more security controls you should consider enabling.
Step 3. Learn your settings
Some common Zoom security settings are listed below, along with recommendations for the most secure setting option for each.
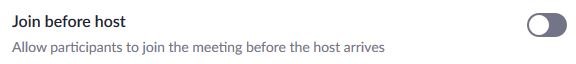
Join before host
Recommendation: Set to “disable.” Highly recommended for all users.
Disabling “Join Before Host” prevents people from entering your Zoom meeting area if you are not in it. Anyone who accesses your meeting link will be placed on hold until you enter, then they will automatically be admitted with you.
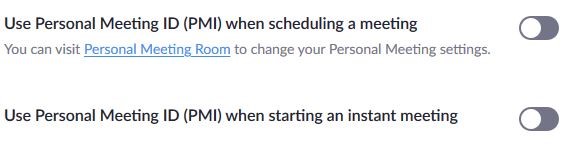
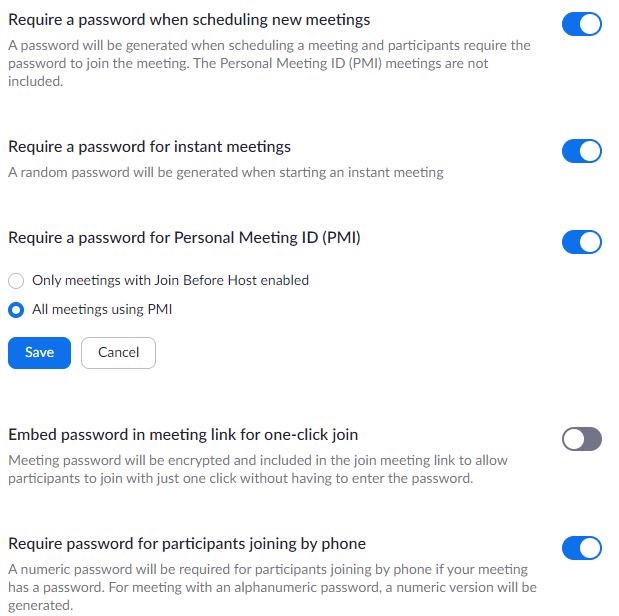
Personal Meeting ID (PMI)
Recommendation: Set to “disable.” Highly recommended for all users.
Zoom allows you to set a consistent meeting ID, just like your office phone number. You can then give out the same meeting ID for all meetings, making it easy for attendees to remember the link.
This can also make it easy for unwanted attendees to enter your meetings and cause disruption, however. There is software that will crawl the internet and automatically collect PMI’s for attackers to use later. To maximize security, avoid using a personal meeting ID. Instead, allow Zoom to generate unique meeting IDs for each meeting you host.
If you do decide use a PMI, require a password for entry (see below) and/or avoid sharing your link in public places like social media, email signatures or other public forums.
Meeting passwords
Recommendation: Set to Enable. Highly recommended for all users.
Requiring participants to enter passwords in addition to clicking on a meeting link does make it tougher for participants to enter your Zoom meetings. However, it is a powerful way to stop unwanted attendees.
Avoid sharing meeting links and passwords on public forums if you are concerned about unwanted intrusion.
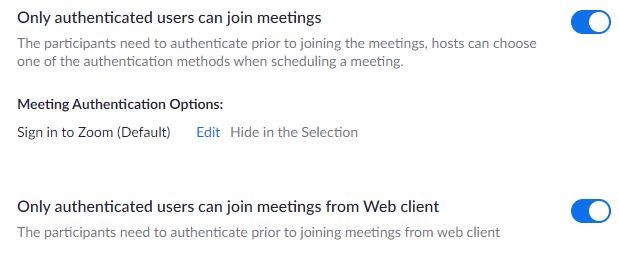
Participant login
Recommendation: Participant login is recommended for meetings where very tight security is needed and attendees come from UGA only.
Enable the “only authenticated users” setting for very high security. Enabling this option will require anyone attending your meeting to have an existing Zoom account and log into that account with their username and password before being allowed into your meeting. Only authenticated Zoom account holders will be permitted access. This is not a good option for meetings with external participants outside of UGA and is best for UGA-only meetings where you know everyone attending will already have set up their own Zoom accounts through UGA.
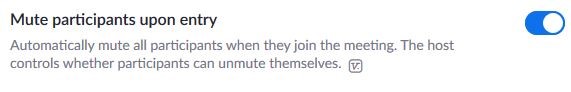
Mute participants
Recommendation: As needed.
Select this option to automatically mute all participants when they enter your meeting room. They can still manually un-mute in order to speak if you allow it, but it will reduce the unwanted noise and conversation from those unaware that their mics are open.
Screen sharing
Recommendation: Set to “host only.” Highly recommended for all users.
Setting the screen sharing setting to “Host Only” will prevent “Zoombombing.”
One of the primary ways to secure a meeting is to prevent participants from sharing content from their own PCs to the entire meeting without any restriction. Verify these settings are enabled (they are by default), so that they require the host to specifically grant permission to other participants before they can share anything to the meeting.
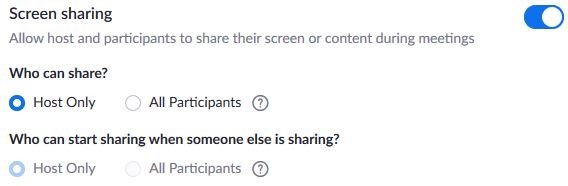
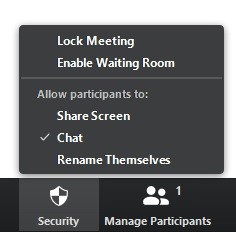
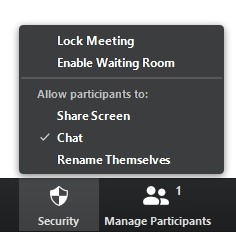
While a meeting is in progress, you can adjust this permission from the Security tab in the meeting controls if one or more participants need to share their screen. You can disable the option when participant sharing is complete.
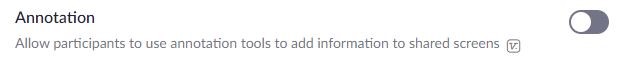
Annotation
Recommendation: Set to “disable.” Highly recommended for large meetings with many unknown participants. Optional for standard, regular meetings where participants are known.
Disable Annotation to prevent participants from drawing or marking on shared content in your meetings. Someone could potentially draw inappropriate content or create other distractions.
You can turn this setting on if you are meeting for specific purposes where this would be needed for collaboration and your participants are all known to you. Enable it before starting your meeting if you do need to use it, then disable after the meeting is over.
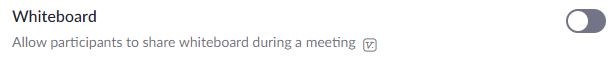
Whiteboard
Recommendation: Set to “disable.” Highly recommended for large meetings with many unknown participants. Optional for standard, regular meetings where participants are known.
Turn this off to prevent participants from drawing and marking on a shared whiteboard. Someone could potentially draw inappropriate content or create other distractions.
You can enable this setting if you are meeting for specific purposes where it would be needed for collaboration and your participants are all known to you. Enable it before starting your meeting if you do need to use it, then disable after it’s over.
Kick out users
Recommendation: Highly recommended for all users.
In the event an unwanted participant enters your session, you can forcibly remove them. During a meeting, click the Manage Participants button at the bottom of the Zoom meeting window, locate the offending person, hover the mouse over their name, select More, Remove and confirm. I
n order to ensure they can’t re-enter your room after being kicked out, you need to confirm your settings are set as shown.

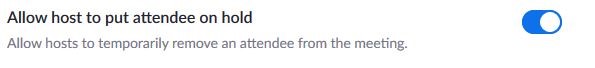
Put attendee(s) on hold
Recommendation: Set to “enable.” Recommended for all users.
The host can temporarily remove a person if the “Put Attendee on Hold” setting is enabled. During a meeting, click the Manage Participants button at the bottom of the Zoom meeting window, locate the offending person, hover the mouse over their name and select More, Put on Hold. This allows the presenter to continue the meeting without the selected participant(s) seeing or hearing what is going on.
Common use cases for this setting include interviewers wanting to deliberate on a candidate, a dissertation committee deliberating on a doctoral candidate, or a meditation session. Repeat the process and choose “Take off hold” to return the participant to the meeting. For this feature to be available during meetings, this setting must be enabled.
Lock your meetings
Recommendation: Recommended for meetings without a lot of participants coming and going, or when you know everyone is present.
After all of your participants join, you can lock additional attendees out so no one else may enter the meeting even if they have the meeting ID and password. Click the Security tab at the bottom of the Zoom meeting window, and select the Lock Meeting option. You will see “Meeting Locked” at the top of the meeting window next to your Zoom Meeting ID. Repeat the process to unlock the meeting if you need to allow someone else to join. If someone leaves your meeting for some reason, they will not be able to get back in if the meeting is locked.
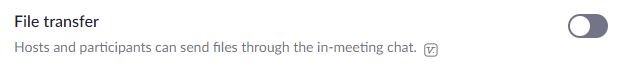
Disable file transfer
Recommendation: Set to “disable.” Highly recommended for large meetings with many unknown participants. Optional for standard, regular meetings where participants are known.
Participants can transfer files within the chat area. This could allow malicious participants to send viral or harmful files disguised as a document or other known file type which any or all participants could then choose to download and open. If you have meetings with large numbers of people many of whom you do not know, it is recommended you disable this feature.
Waiting room
Recommendation: Set to “enable.” Then use on a per-meeting basis if your meeting link is public and/or if you are not using a password for your meetings. Waiting rooms can be difficult to manage for large meetings.
The waiting room feature prevents users from entering your meeting room until you specifically allow them in. Until then, users are placed in an empty area with a message that host will admit them soon. As a host, you will be notified that an attendee is waiting, and you will be given the option to admit them.
Enable the waiting room setting in the settings area of your account to make the option available in your meetings.
Note that you must also select “Enable Waiting Room” in the Security tab of a particular meeting for the setting to take effect. You can toggle it on and off from the Security tab in your meetings as needed.
For large meetings, it works well to have two people “running” the Zoom meeting. One will do the presentation, and another person can handle the waiting room.

Please Note: Zoom has made frequent updates and changes to its settings and features. These options are current as of writing but are subject to change without notice.
For assistance with Zoom or to arrange a tutorial contact your OIT IT rep or the OIT Service Desk: 706-542-2139 oithelp@uga.edu